Is SQL Injection Still Relevant in 2026?
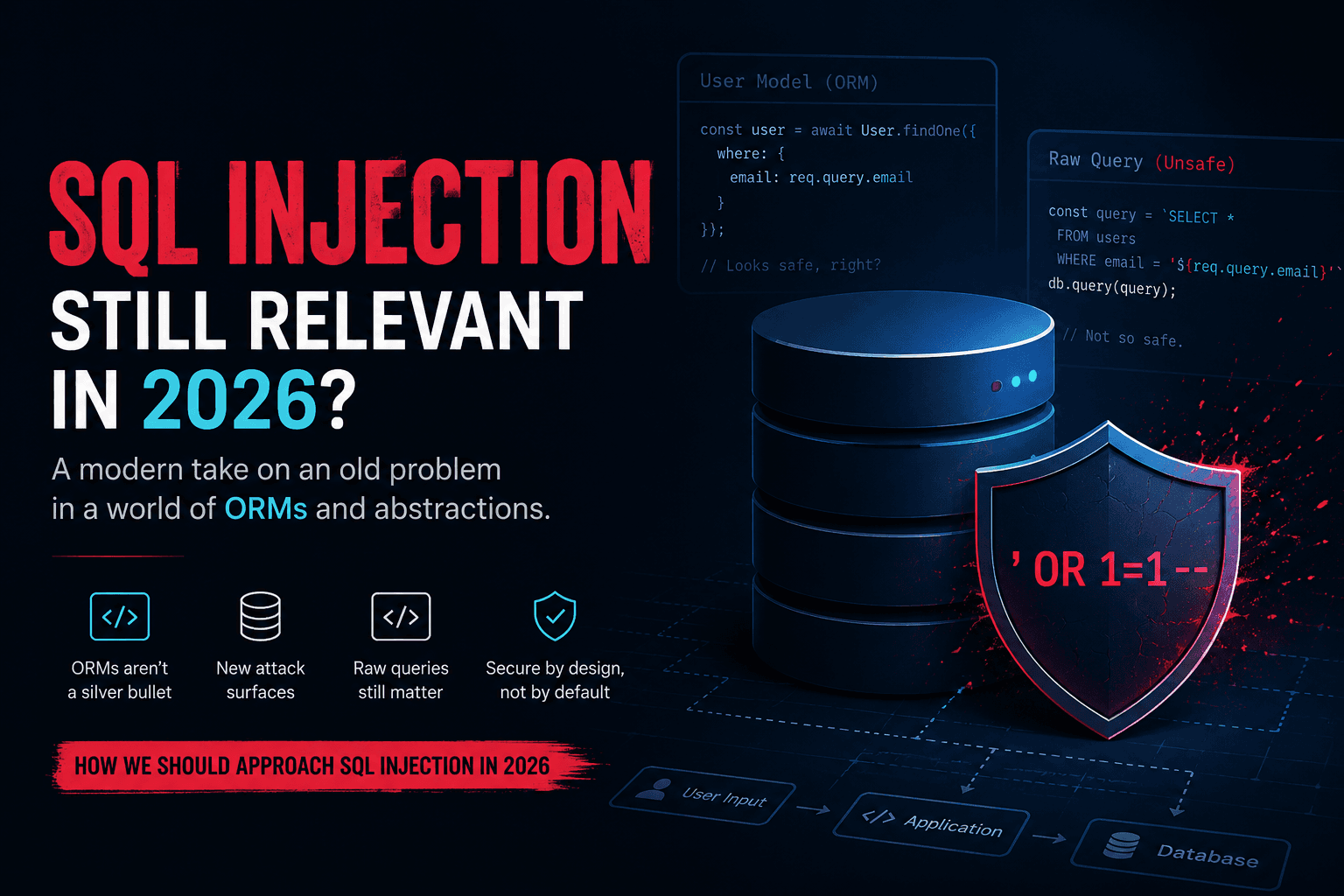
While learning about SQL Injection recently, I had a genuine question in mind:
If modern applications use ORMs everywhere, why should we still care about SQL Injection?
At first glance, it feels outdated. Most modern stacks today use frameworks like Django ORM, SQLAlchemy, Hibernate, Prisma, Sequelize, Entity Framework, and many others. Prepared statements are common. Security awareness is much better than it used to be.
So shouldn’t SQL Injection be “solved” by now?
Turns out, not really.
The interesting part is that SQL Injection today rarely happens because developers write SELECT * FROM users WHERE username=' + input + ' manually like old tutorials show. The real issue is how ORMs are used in production systems.
A few things stood out to me:
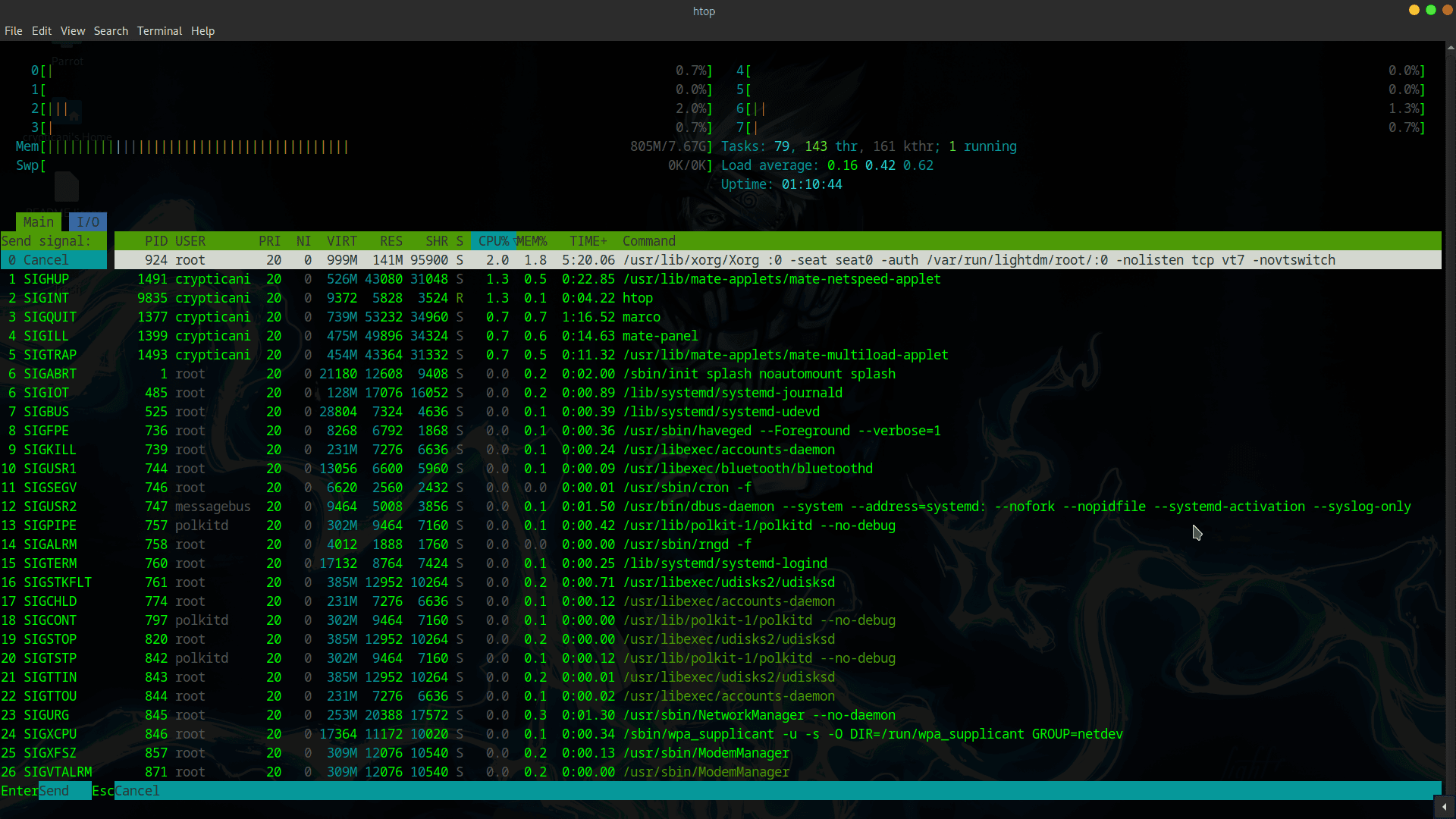
Developers often mix raw SQL with ORM queries for performance or flexibility.
Teams assume “we use an ORM, so we are safe.”
Legacy codebases still exist everywhere.
Dynamic query builders and filters can quietly become injection points.
Security reviews around database code are sometimes skipped because the ORM creates a false sense of safety.
In other words, the attack surface evolved — it didn’t disappear.
I think the way we should approach SQL Injection in 2026 is also different from how it was taught years ago.
Instead of only practicing UNION-based payloads on intentionally vulnerable apps, it makes more sense to understand:
How ORMs internally generate queriesWhere developers bypass ORM protections
Unsafe raw query patterns
Dynamic filtering/search implementations
Second-order SQL injection
JSON/GraphQL/database abstraction edge cases
How modern APIs interact with databases
The goal is no longer just “dump the database.” The goal is understanding how data flows from user input to query execution in modern architectures.
SQL Injection is not dead. It just moved higher up the abstraction layer.